Secure Access
InstaSafe ZTAA provides seamless and secure remote access to internal applications for users by using Software Defined Perimeter (SDP) principles that reduce cybersecurity risks and improves compliance by ensuring applications are hidden, while at the same time allowing access to authorized users and devices after several authentication steps are performed.
All ZTAA configurations and security policies can be deployed, managed and monitored from a central Admin console irrespective of where the applications are hosted. The intuitive console provides a powerful logging and reporting engine.
A guided approach highlighting the steps an admin has to follow is provided upon logging into the console to ensure ease of deployment.
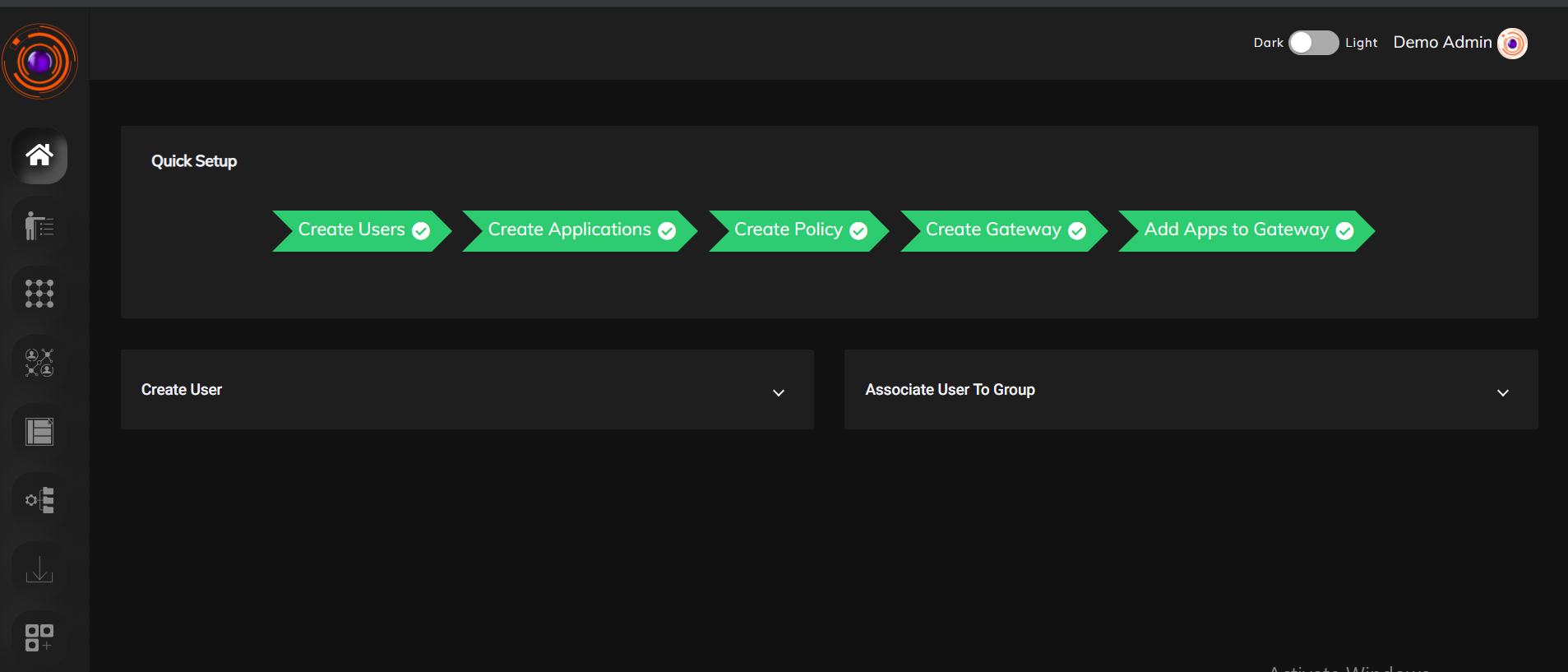
Configuring Secure Access for users
-
Create profile for your users. User profile can be created directly or be imported from existing Active Directory server.
-
Users can be grouped into User groups based on their roles to make administration easier.
-
Create the application which you want to allow access to.
-
Create Data Set for parameters you want to create access control rules with.
-
Create Gateway based on requirement.